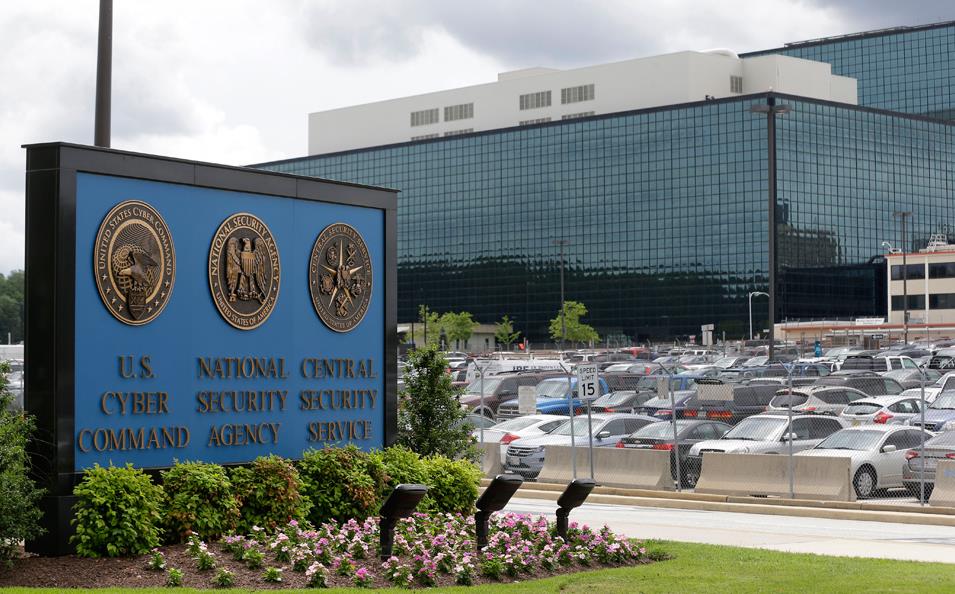
In the tug-of-war between the government and U.S. companies over whether firms should hold a key to unlock encrypted communications, a frequent argument of technologists and privacy experts is that maintaining such a key poses a security threat.
But on Thursday, FBI Director James B. Comey pointed out that a number of major Internet companies do just that “so they can read our e-mails and send us ads.”
And, he said: “I’ve never heard anybody say those companies are fundamentally insecure and fatally flawed from a security perspective.”
Comey was airing a new line of government argument in the year-old public debate over the desirability of compelling Internet companies to provide a way for law enforcement to have access to decrypted communications.
Although he didn’t name names, he was alluding to major e-mail providers Google and Yahoo, which both encrypt customers’ e-mails as they fly between servers, but decrypt them once they land in order to scan them and serve customers relevant ads.
Comey, who spoke at a cyberthreats hearing held by the House Intelligence Committee, has been a leading voice advancing the concerns of law enforcement that the growing trend of strong encryption — where devices and some communications are encrypted and companies do not hold the keys to decode them — will increasingly leave criminal investigators in the dark.
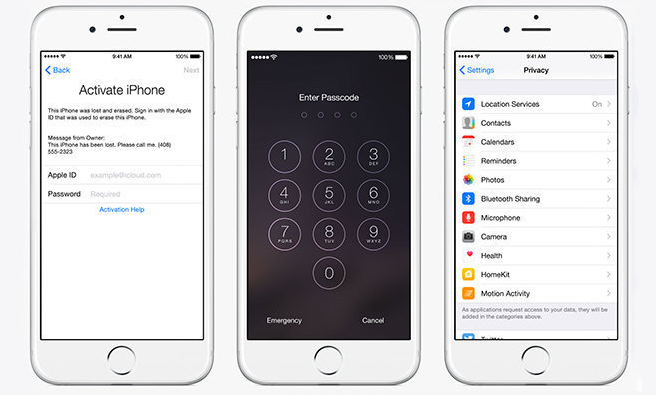
The current debate, which echoes a bitter argument over encryption in the 1990s, was triggered by Apple’s announcement last September that it would expand the use of a method of encryption on its mobile operating system in which it did not hold a key. That meant Apple could no longer unlock troves of photos and other data stored on iPhones and iPads where the user had turned off the automatic backup to Apple’s servers. Such data “at rest” is useful in criminal investigations.
Of great concern to counterterrorism officials are communications encrypted in transit, such as text and instant messages, where the companies do not hold a key and where users have turned off automatic backups. Such end-to-end encryption is a feature of Apple’s iMessage and FaceTime — a video phone-call system, as well as Open Whisper Systems’ Signal, and WhatsApp — both instant message platforms.
But stored commercial e-mail is largely either unencrypted, or encrypted with a key known to the provider, Christopher Soghoian, principal technologist at the American Civil Liberties Union, said in an interview. And that’s a recipe for insecurity, he said.
“Any data that’s either unencrypted or encrypted with a key known to another party is inherently more vulnerable,” he said. He added that Google and Yahoo have been criticized for their lack of e-mail security, and the Chinese breach of Gmail announced in 2010 was a case in point.
During the hearing, Comey said that the bureau was “having some very healthy discussions” with companies on the issue. “I would imagine there might be many, many solutions depending upon whether you’re an enormous company in this business, or a tiny company in that business. I just think we haven’t given it the shot it deserves.”
Rep. Adam Schiff (D-Calif.) noted that the tech firms have stiff global competition. Other companies are offering encrypted platforms that customers might choose. “So what do we achieve, apart from harming our economic interests, by insisting on a key?” he said.
Comey said he thought that part of the solution would be “an international set of norms” in which other countries join with the United States to establish a rule that companies should be able to provide law enforcement with communications in the clear. “I hear from our allies all the time,” he said. “The French want the same thing. The Germans. The British. So I think that’s something that could be done.”
Soghoian noted, however, that more and more encryption platforms are being made available on the Internet for free by individuals or groups of open-source developers in the United States and Europe, which will make it difficult to regulate them.