During last night’s democratic debate we were once again inundated with calls from politicians who sought compromise from Silicon Valley in its on-going battle with terrorism. Encryption was the point of contention.
The candidates echoed previous statements regarding the dangerous world we live in. The reason for danger, or so it goes, is the inability of law enforcement to pursue threats from terrorists, both domestic and international, who are increasingly reliant on encryption to communicate.
The sentiment is true, albeit misguided, but more on that in a moment.
Currently, the argument is painted as black and white, a “you’re either for us, or against us” exchange that leaves average Americans scratching their collective heads wondering why Silicon Valley isn’t stepping up the fight against terrorism by cooperating with government.
Arguments, even this one, are rarely binary.
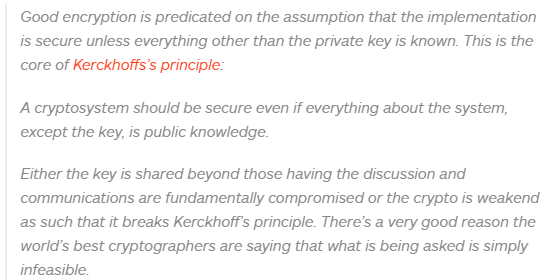
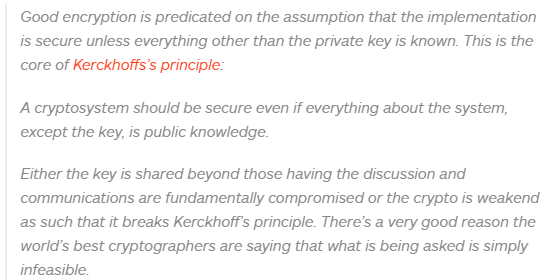
In fact, from a security standpoint, the compromise the government seeks is impossible.
“Technically, there is no such backdoor that only the government can access,” says cyber security expert Swati Khandelwal of The Hacker News. “If surveillance tools can exploit ‘vulnerability by design,’ then an attacker who gained access to it would enjoy the same privilege.”
Microsoft MVP of developer security, Troy Hunt adds:
The encryption smear campaign
For all that encryption does for us, it has become a quagmire of political talking points and general misuderstanding by citizens and I’d argue, politicians.
“The truth is that encryption is a tool that is used for good, by all of us who use the internet everyday,” says famed computer security expert Graham Cluley.
“Encryption is a tool for freedom. Freedom to express yourself. Freedom to be private. Freedom to keep your personal data out of the hands of hackers.”
The term itself has become a bit of a paradox. Numbers paint a picture of citizens who think it’s important but have no real idea of how and where it protects them.
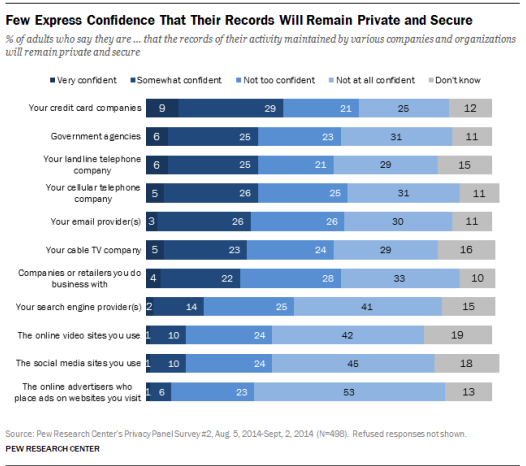
According to a Pew Research report, fewer than 40 percent of US citizens feel their data is safe online, yet only 10 percent of adults say they’ve used encrypted phone calls, text messages or email and 9 percent have tried to cover online footprints with a proxy, VPN or TOR.
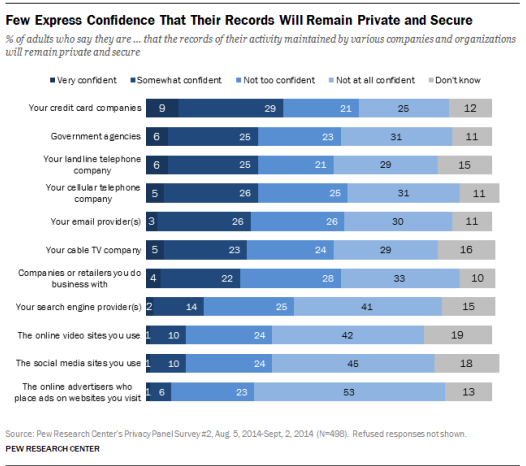
These numbers demonstrate a fundamental misunderstanding of encryption and further detail its public perception.
It is, after all, only natural to attempt to protect yourself when you can foresee a threat, yet US citizens have a rather apathetic view of the very technology that could make them safer online.
According to the experts in the field that I spoke with, they all seem to agree that there are two reasons people aren’t taking more steps to remain secure.
- Barrier to entry: These technologies feature a lot of jargon and many aren’t all that user friendly. PGP for example, the email encryption technology used by Edward Snowden to communicate with Laura Poitras and Glenn Greenwald, involves relatively-foreign setup instructions for your average citizen.
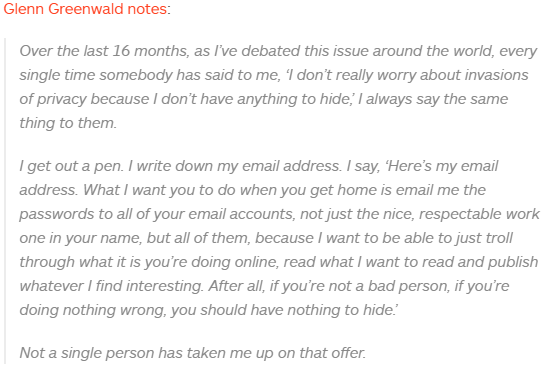
- Negative connotation: Most Americans don’t realize they use encryption every day of their lives. Instead, they know encryption as the tool terrorists use to send private messages, recruit new members and spread propaganda online. This is largely due to the on-going encryption debate.
This debate, whether planned or incidental, is doubling as a smear campaign for the very suite of tools that keeps our online lives secure.
It wasn’t mentioned amongst our expert panel, but I believe there is a third reason that the general public isn’t taking action to better secure themselves online.
Silicon Valley isn’t backing down
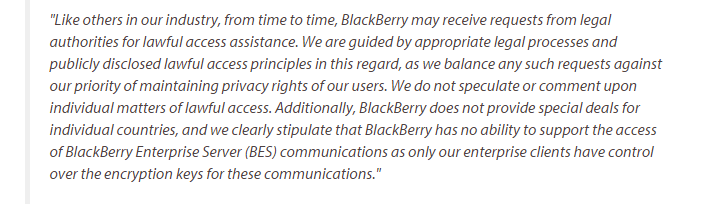
So far, the term “debate” may be more of a misnomer. Silicon Valley isn’t debating anything. Furthermore, there may not be anything to debate in the first place.
You can’t “compromise” on weakened security; either it’s secure, or it isn’t.
This veritable Pandora’s Box the US Government wants to explore would lead to backdoor access into our personal lives not just for the government but for hackers and bad actors around the globe. And once you open it, there’s no going back.
“You can’t have secure encryption with a government backdoor. Those two things are mutually exclusive,” notes Cyber security thought leader at Script Rock, Jon Hendren. “‘Working with Silicon Valley’ is essentially code for ‘Giving us a backdoor into the accounts, data, and personal lives of users’ and should be totally unacceptable to anyone who even remotely values their privacy.”
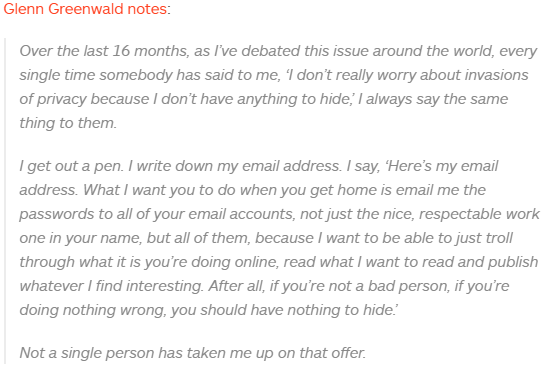
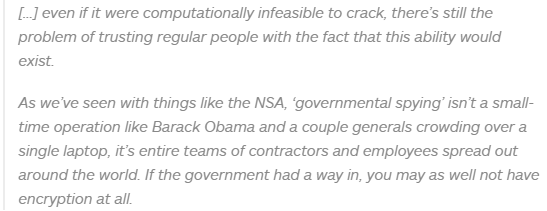
There’s also the issue of trust. Even if these backdoors weren’t creating vulnerabilities for bad actors to attack, do we trust the government with our data in the first place?
Our expert panel says, no.
“Handing over such backdoor access to the government would also require an extraordinary degree of trust,” says Khandelwal, “but data breaches like OPM [Office of Personnel Management] proved that government agencies cannot be trusted to keep these backdoor keys safe from hackers.”
Hendren adds:
Compromise, in this case, is a rather contentious point of view. The compromise the government seeks isn’t a compromise at all; it’s a major loss of privacy and security as it relates to citizens around the globe.
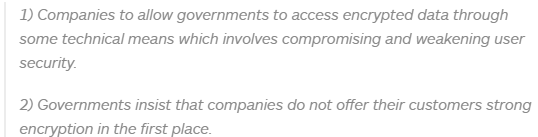
Clulely shows us how this “compromise” might play out.
The third option is to keep things as they are, or further expound on the efforts to secure the internet.
There really is no middle ground in this debate.
Would providing a backdoor help to fight terrorism?
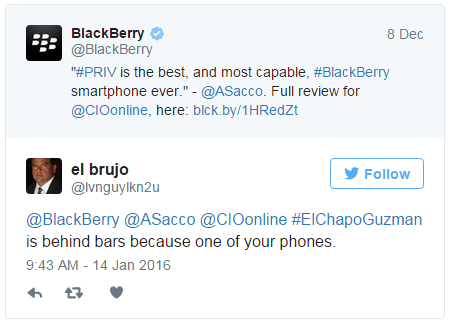
Since fighting terrorism is the narrative in which the government is using to attempt to stamp out encryption, you have to wonder if encryption is truly the thorn in its side that government officials claim it to be.
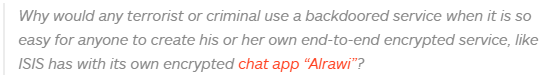
It’s well-known that ISIS is using encrypted chat apps, like Telegram, to plan attacks and communicate without detection, but would a backdoor have any effect on the surveillance or capture of extremists?
“A backdoor would also have a limited window of efficacy– bad guys would avoid it once that cat is out of the bag,” says Hendren. “This would have the effect of pushing bad actors further down into more subtle and unconventional ways of communication that counter-terrorists might not be aware of, or watching out for, lessening our visibility overall.”
Khandelwal agrees:
It’s naive to believe that an extremist group that recruits and grooms new members from the keyboard, not the battlefield, isn’t tech savvy enough to find a new means of communication as current ones become compromised.
The privacy debate isn’t going anywhere. Moreover, the ambient noise created by politicians spouting off about technologies they don’t understand should grow in volume as we near the primaries and then the general election.
What’s clear though, is that this isn’t a debate and that Silicon Valley has no means to compromise.
Without compromise, the government is left with but one recourse, policy. One can only hope that we have leaders and citizens who better understand the need for encryption before that day comes.
In this debate, no one is compromising — or compromised — but the end user.