Keeping customer data secure is of utmost importance in any organization. Therefore, compliance with security standards is vital.
In today’s world, a company cannot afford to experience breaches of customer information, transactional data or other important business information given the volume of business taking place online and the consequences of such breaches.
When considering collocation at a commercial data centre, compliance to global security standards, such as the Payment Card Industry Data Security Standard (PCI DSS) and Information Security Standards, should feature as a key selection criteria.
Speaking about the measures put in place to ensure security of data, the CEO of MainOne, Funke Opeke, said that “security in the Data Centre cannot be over emphasised and MainOne’s Tier III Data Centre, MDX-I, recently subjected its operations to rigorous process improvements and audits to ensure compliance and certification on these key security standards.”
She confirmed that MDX-I was certified following a comprehensive ISO27001 audit carried out by British Standard Institution (BSI) group; a business standards company that helps organisations all over the world make excellence a habit. “The PCI DSS assessment was conducted by Digital Jewals Limited, a PCIDSS QSA and an information value chain company which also provided end-to-end support in preparing the Data Centre for certification to both standards. The audits measure the facilities at the Data Centre according to several strict criteria including physical access controls as well as information security policies, procedures and infrastructure”, she said.
Compromised data affects customers, business partners and financial institutions as a single incident and can severely damage a company’s reputation and its ability to conduct business effectively. Data breaches lead to catastrophic loss of sales due to damaged reputation and business relationships, lawsuits, insurance claims, cancelled accounts, payment card issuer fines and possible government fines or other liabilities.
In order to avoid possible breaches, collocating equipment with a provider that is compliant to global standards provides assurance that your systems and sensitive customer information remains secure.
Opeke reaffirmed that the “PCI DSS accreditation is the most comprehensive, internationally recognised data security consisting of robust and comprehensive standards, and supporting materials to enhance payment card data security. These include a framework of specifications, tools, measurements and support resources to help organizations ensure the safe handling of cardholder information at every step. It provides an actionable framework for developing a robust payment card data security process including prevention, detection and appropriate reaction to security incidents”.
In addition to that, the CEO made mention that MXD-I has the ISO 27001 security certification, a globally recognised Information Security Management System (ISMS) standard, which ensures the right information security management environment, procedures and policies to ensure that it is able to provide a high degree of security and assurance to customers.
According to her, outsourcing Data Centre operations to a collocation provider that imbibes global security policies and procedures to mitigate data breaches remains the best choice for any business.
“We are the first data centre in Nigeria to be PDCI DSS certified. This is the same security certification banks have to get when they are at the highest levels of performance for the security of their customers financial data so if people are comfortable enough to provide personal data to banks, why wouldn’t they have confidence in a certified data centre that is ready to submit itself to external audit and verification to show that it is in compliance with standards. This actually gives you the peace of mind that you get the secure environment you need as opposed to the one that you are building in house but may not have adequate resources to sustain on an ongoing basis. In this challenging environment, wouldn’t you rather have a certified partner to handle your data”, she said.
Managing Director of Epinec Nigeria Limited, an ICT company in partnership with Microsoft, Obi Ibeto was asked about how secure data centers are. He said “access to the physical data centre is highly restricted. With biometric readers, motion sensors, 24-hour secured access, video surveillance, and many other security features – in my opinion – the warehouses look like something from a James Bond movie”.
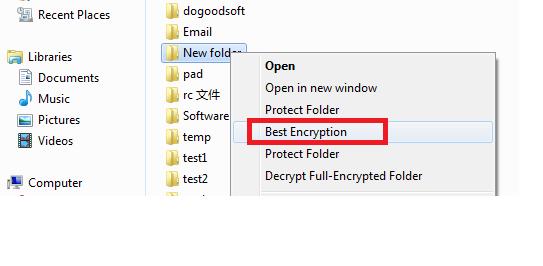


 The secret disk can be used just like a normal disk, which is easy for people to save private files.
The secret disk can be used just like a normal disk, which is easy for people to save private files.
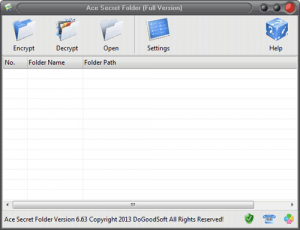
 Free version of Best Encryption Expert can be used free of charge for 7 days. During the trial, some features like password restore and First Aid Center is not available. Besides, it can only decrypt an already encrypted file/folder when the trial expires.
Free version of Best Encryption Expert can be used free of charge for 7 days. During the trial, some features like password restore and First Aid Center is not available. Besides, it can only decrypt an already encrypted file/folder when the trial expires.