Law-enforcement officials are running up against a new hurdle in their investigations: the encrypted smartphone.
Officials say they have been unable to unlock the phones of two homicide victims in recent months, hindering their ability to learn whom those victims contacted in their final hours. Even more common, say prosecutors from New York, Boston and elsewhere, are locked phones owned by suspects, who refuse to turn over passcodes.
Manhattan District Attorney Cyrus Vance says his office had 101 iPhones that it couldn’t access as of the end of August, the latest data available.
The disclosures are the latest twist in a continuing dispute between law-enforcement officials and Apple Inc. and Google Inc., after the two tech companies released software last year that encrypted more data on new smartphones. The clash highlights the challenge of balancing the privacy of phone users with law enforcement’s ability to solve crimes.
“Law enforcement is already feeling the effects of these changes,” Hillar Moore, the district attorney in Baton Rouge, La., wrote to the Senate Judiciary Committee in July. Mr. Moore is investigating a homicide where the victim’s phone is locked. He is one of 16 prosecutors to send letters to the committee calling for back doors into encrypted devices for law enforcement.
The comments are significant because, until now, the debate over encrypted smartphones has been carried by federal officials. But local police and prosecutors handle the overwhelming share of crimes in the U.S., and district attorneys say encryption gives bad guys an edge.
Encrypted phones belonging to victims further complicate the issue, because some families want investigators to have access to the phones.
“Even if people are not terribly sympathetic to law-enforcement arguments, this situation might cause them to think differently,” said Paul Ohm, a Georgetown University Law Center professor and former prosecutor.
Last week, Federal Bureau of Investigation Director James Comey told a Senate hearing that the administration doesn’t want Congress to force companies to rewrite their encryption code. “The administration is not seeking legislation at this time,” White House National Security Council spokesman Mark Stroh said in a written statement Monday.
Some independent experts say the handful of cases that have emerged so far isn’t enough to prove that phone encryption has altered the balance between law enforcement and privacy. In many cases, they say, investigators can obtain the encrypted information elsewhere, from telephone companies, or because the data was backed up on corporate computers.
—————————————————————————————————————————————————–
‘In the past this would have been easy for us. We would have an avenue for this information, we’d get a subpoena, obtain a record, further our investigation.’
—————————————————————————————————————————————————–
“It depends on what the success rate is of getting around this technology,” said Orin Kerr, a George Washington Law professor.
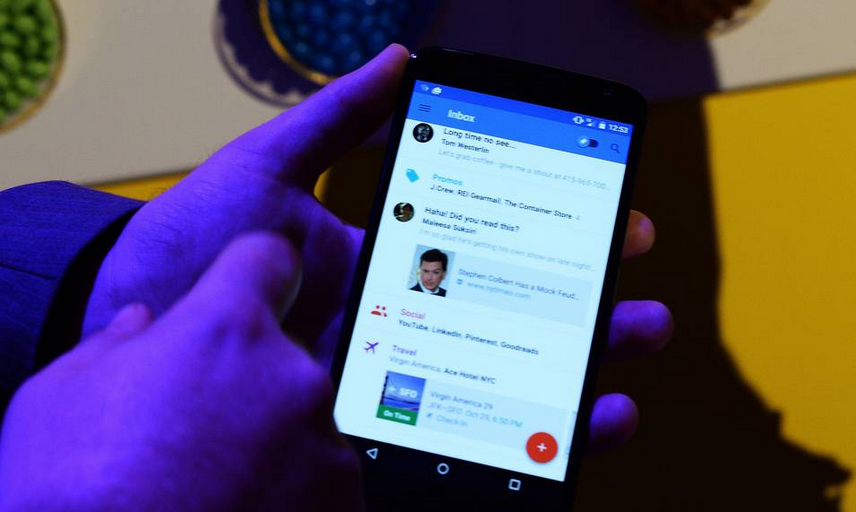
Apple encrypted phones by default beginning with iOS 8, the version of its mobile-operating system released last fall. The decision came amid public pressure following former national-security contractor Edward Snowden’s revelations of tech-company cooperation with government surveillance.
With iOS 8, and the newly released iOS 9, Apple says it cannot unlock a device with a passcode. That means Apple cannot provide information to the government on users’ text messages, photos, contacts and phone calls that don’t go over a telephone network. Data that isn’t backed up elsewhere is accessible only on the password-protected phone.
“We have the greatest respect for law enforcement and by following the appropriate legal process, we provide the relevant information we have available to help,” Apple wrote in a statement to The Wall Street Journal.
Apple Chief Executive Tim Cook is an advocate of encryption. “Let me be crystal clear: Weakening encryption, or taking it away, harms good people that are using it for the right reasons,” he said at a conference earlier this year.
Only some phones, such as the Nexus 6 and the Nexus 9, running Google’s Android Lollipop system are encrypted by default. Google declined to comment about the role of encryption in police investigations.
Three of the 16 district attorneys who wrote to the Senate—from Boston, Baton Rouge and Brooklyn—told the Journal they were aware of cases where encrypted phones had hindered investigations. Investigators in Manhattan and Cook County in Illinois also have cases dealing with encrypted phones. Investigators say, however, they have no way of knowing whether or not the locked phones contain valuable evidence.
Mr. Moore, of Baton Rouge, thinks there might be important information on a victim’s phone. But he can’t access it.
Brittany Mills of Baton Rouge used her iPhone 5s for everything from sending iMessages to writing a diary, and she didn’t own a computer, her mother said. Ms. Mills, a 28-year-old patient caregiver, was shot to death at her door in April when she was eight months pregnant.
Police submitted a device and account information subpoena to Apple, which responded that it couldn’t access anything from the device because it was running iOS 8.2. Mr. Moore thinks the iCloud data Apple turned over won’t be helpful because the most recent backup was in February, two months before her death. The records he obtained of her phone calls yielded nothing.
“When something as horrible as this happens to a person, there should be no roadblock in the way for law enforcement to get in there and catch the person as quickly as possible,” said Barbara Mills, Brittany Mills’s mother.
Investigators in Evanston, Ill., are equally stumped by the death of Ray C. Owens, 27. Mr. Owens was found shot to death in June with two phones police say belonged to him, an encrypted iPhone 6 and a Samsung Galaxy S6 running Android. A police spokesman said the Samsung phone is at a forensics lab, where they are trying to determine if it is encrypted.
The records that police obtained from Apple and service providers had no useful information, he added. Now the investigation is at a standstill.
“In the past this would have been easy for us,” said Evanston Police Commander Joseph Dugan. “We would have an avenue for this information, we’d get a subpoena, obtain a record, further our investigation.”
Barbara Mills is committed to making sure more families don’t have to see cases go unsolved because of phone encryption. “Any time you have a situation of this magnitude, if you can’t depend on law enforcement, who can you depend on?”