Encryption is an important aspect which governs not just the communications but also the storage. When data is in motion there are some methods/ protocols which facilitate end-to-end encryption:
1. VPN
2. Remote Server Connectivity viz. RDP, SSH
3. Internet based Voice/ Messaging Communications
4. email communication
5. Communications between Wearables and their Host devices
6. Web-Services providing encryption services viz. Etherpad, Gist
However, when it concerns data at rest ie. data stored on the disk, there are numerous scenarios which fall under the purview of encryption:
1. On the Fly Disk Encryption which may also include the entire OS
2. Password protection of files
3. email Message Encryption
4. Full disk-encryption by Smartphones
Recently, Government of India released its version of Draft for National Encryption Policy and within 24 hours of releasing it, they have withdrawn it, however with a promise the policy will be re-drafted and re-released.
In these 24 hours, all those involved in IT security of the Indian Internet Security forum took up the cause of protecting user privacy, reprimanding the government for ill conceived draft of National Encryption Policy. Their efforts resulted in forcing the government to revoke the draft proposal and contemplate on a better proposal.
According to the draft, B2B/ B2C and C2B, sector shall use encryption algorithms and key sizes as prescribed by the government, moreover, according to the draft:
“On demand, the user shall be able to reproduce the same Plain text and encrypted text pairs using the software/ hardware used to produce the encrypted text from the given plain text. Such plain text information shall be stored by the user/ organization/ agency for 90 days from the date of transaction and made available to Law Enforcement Agencies as and when demanded in line with the provisions of the laws of the country.”
Furthermore, the draft also issued guidelines for communication with foreign entity, “the primary responsibility of providing readable plain-text along with the corresponding Encrypted information shall rest on entity (B or C) located in India.”
The draft policy requires service providers whether irrespective of their country of origin to enter into an agreement with the Government of India and the consumers of these services (Government/ Business/ Citizens) are expected to provide the pain-text/encrypted datasets.
The question is not why, but how would it be technically feasible for a customer to maintain this information, given the fact that encryption was used to secure the data from rogue entities. Storing anything in plain-text for any amount of period, defeats the entire purpose of using encryption except with a solace that the channel used for transmission of data is secured. The draft has set very high and impossible to achieve expectations from every citizen and organization, irrespective of their field of expertise to have knowledge about the internal working of these third party applications, also at the same time they are expected to have knowledge about maintaining the two different data-sets.
Furthermore, the draft also requires anything that has been encrypted by an individual be it his personal documents or communication between two individuals, which interestingly is considered to be a private affair by the rest of the world, to be made available for scrutiny as and when demanded.
Expecting a consumer of various services, irrespective of the fact whether the consumer is an organization or an individual, to understand the internal functionality of each and every service / software and take a conscious decision of maintaining the two separate data-sets is simply not feasible and virtually impossible.
Even though a clarification was issued by the government that
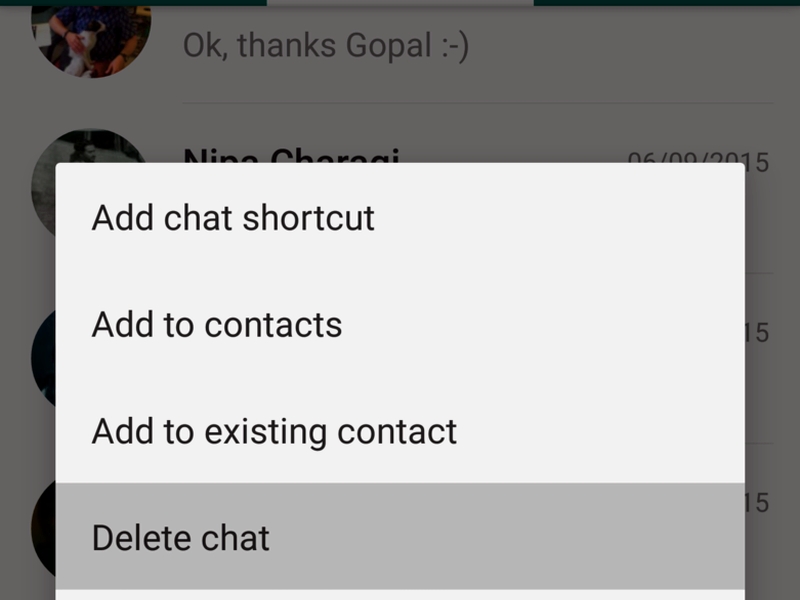
The mass use encryption products, which are currently being used in web applications, social media sites, and social media applications such as Whatsapp, Facebook, Twitter etc.
SSL/TLS encryption products being used in Internet-banking and payment gateways as directed by the Reserve Bank of India
SSL/TLS encryption products being used for e-commerce and password based transactions.
It still raises quite a few eyebrows especially about the intention of the drafting of this National Encryption Policy. Not just the privacy, but also the feasibility and the security are at risk.
The argument until now was about data which resides on your disk, and using these very standards what can we say about the encrypted communication channels/ services? One word summarizes it all “Impossible”. Over the network encryption like VPN/ SSH or to put it simply cloud based services be it of any-type, which lately have made inroads into our lives would be rendered useless and their very existence in India is at risk, not just because it would have been mandatory for all of them to enter into an agreement with the Government of India, but the consumers of these services will also have to maintain a separate copy of the content.
Applications and Service providers who provide Secure Messaging ie, encrypting the voice channels or self-destructing messages, in order to provide better privacy and discourage eavesdropping, would in all probability get banned or might have to remove these features so as to cater to Indian audience. Over and above, how do the policy-makers expect the consumers to comply?
What happens when a person from a different country uses these services in India? Wouldn’t this person be violating the Indian Law and in all probability be considered a criminal?
The draft also requires all the stakeholders to use Symmetric Cryptographic/Encryption products with AES, Triple DES and RC4 encryption algorithms and key sizes up to 256 bits.
Way back in 2011 when Microsoft Researchers discovered a way to break AES based encryption, Triple DES is considered weak, while RC4 is simply not acceptable as an encryption algorithm to any organization. These are age-old encryption algorithms and are never/rarely considered when organizations are drawing up their own encryption policies.
In this age of competition, organizations have their own trade secrets to be guarded, not just from competitors but also from rogue governments. A weakened encryption schema and mandatory storage of encrypted data in its plain text form is nothing less than committing a Harakiri for these organizations. Moreover, by way of an agreement that draft expects the software/ hardware vendors to comply with these encryption restrictions, thereby weakening the overall security of India’s IT infrastructure.
National Encryption Policy should be about setting up of minimum encryption standards for data protection, penalization organizations and institutions for not implementing high encryption standards and protecting the data from pilferage and leakage.
Encryption policy has always had a direct impact on the privacy of an individual and when it used by corporations/ organization, it affects their business/ trade secrets; hence Government should also consider thinking about the various means and ways of implementing/ strengthening the non-existent privacy laws.
As we have been promised that the policy would be re-drafted, let us keep our fingers crossed and hope that better sense prevails.