Fujitsu says it has developed software that uses biometric data directly as the basis for encryption and decryption of data, simplifying and strengthening security systems that rely on biometrics such as fingerprints, retina scans and palm vein scans.
Current security systems that rely on encryption require the management of encryption keys, which are stored on secure smartcards or directly on PCs. Biometric scans can be used as a way of authenticating the user and providing access to those encryption keys in order to decrypt data.
Fujitsu’s system uses elements extracted from the biometric scan itself as a part of a procedure to encrypt the data, making the biometric scan an integral part of the encryption system and removing the need for encryption keys.
That has two big benefits, according to the company.
The lack of encryption keys means there’s no need for smartcards and hackers won’t have anything to find should they break into a network.
The second major benefit comes from biometric data use with cloud services. With current systems, a user’s biometric data is potentially vulnerable as it’s sent over the Internet to allow log-in to a service. Because Fujitsu’s new system uses random numbers to convert the biometric data as part of the encryption and decryption process, unconverted data is not transmitted over a network.
The procedure employs error correction to smooth out slight differences in successive biometric scans that are the result of variations in a user’s position or motion when the scan is taken.
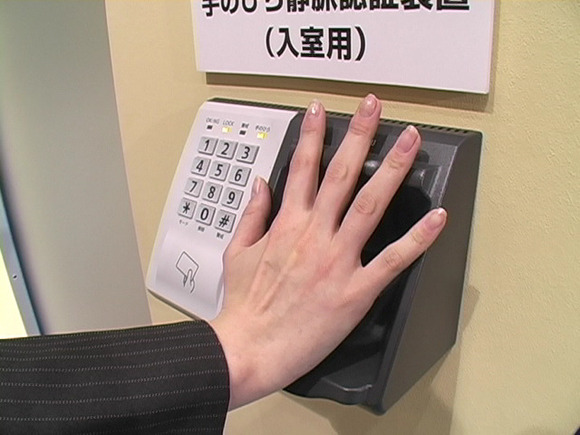
At present, the system has been developed to work with palm vein authentication, a technology that Fujitsu has spent years developing and has already deployed on systems like bank ATMs in Japan. But the company said it could readily be adapted to work with other biometric data such as fingerprints or retina scans.
The software was developed by Fujitsu Laboratories and two Japanese universities, Kyushu University and Saitama University, and is being presented this week at the 8th International Symposium on Foundations and Practice of Security in Clermont-Ferrand, France.