Utility generates unscrambling key.
Users whose data has been held to ransom by the Petya malware now have an option to decrypt the information, thanks to a new tool that generates an unscrambling key.
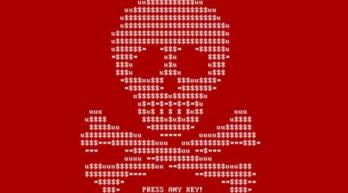
Petya appeared around March this year. Once executed with Windows administrator privileges, Petya rewrites the master boot record on the computer’s hard drive, crashes the operating system and on restart, scrambles the data on the disk while masquerading as the CHKDSK file consistency utility.
The Petya attackers then demand approximately A$555 in ransom, payable in BItcoin, to provide a decryption key for the locked system.
An anonymous security researcher using the Twitter handle leo_and_stone has now cracked the encryption Petya uses, the Salsa10 function created by DJ Bernstein in 2004.
Decrypting hard disks scrambled with Petya using the tool is a relatively complex operation. The tool requires data from an eight-byte nonce (random, use-once number) file and a 512-byte sector from the hard disk to be input into a website to generate the the decryption key.
This means the Petya-infected hard drive has to be removed from the victim computer, and the small amount of data needed for the decryptor read and copied with low-level system utilities.
Once that is done, the scrambled hard drive has to be reinserted into a computer to bring up the Petya ransom demand screen, at which stage the decryption key can be entered.
Tech support site Bleeping Computer, run by computer forensics specialist Lawrence Abrams, reported success with Leo Stone’s Petya decryptor, with keys being generated in just seconds.
A Windows tool to make it easier to extract the verification data and nonce was also created by researcher Fabian Wosar from security vendor Emsisoft.